Multi-tenant PBX is not simply a way to save server costs. It is the architectural decision that determines whether a hosted telephony business can scale to hundreds of customers, maintain per-customer isolation, and deliver profitable margins without a corresponding explosion in operational overhead. The hosted PBX market generated an estimated USD 13.2 billion in revenue in 2024, and it is projected to grow at a CAGR of 16.8% from 2025 to 2032. Service providers and technical evaluators who understand how multi-tenancy works at a structural level are far better positioned to build and operate in that market than those who treat it as a generic checkbox.
What Is a Multi-Tenant PBX?
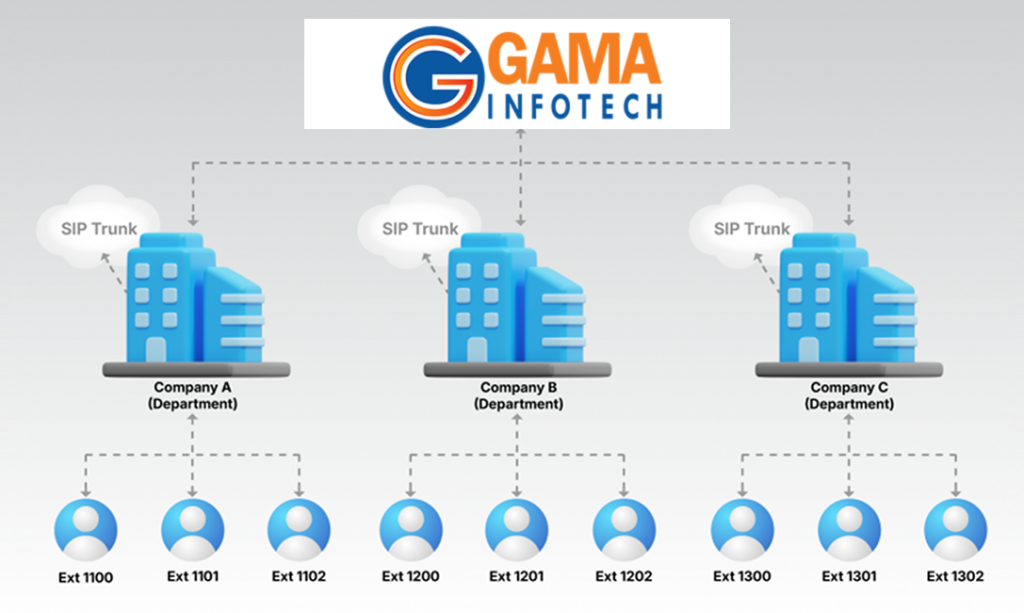
A multi-tenant PBX is a single hosted telephony platform that simultaneously serves multiple independent business customers—called tenants—on shared underlying infrastructure, while keeping each customer’s data, configuration, and call flows completely separated from every other.
A multi-tenant PBX is a phone system where multiple businesses share the same PBX infrastructure. Each tenant is isolated at the software level, with separate user accounts, extensions, call flows, and configurations—but all share the same core system, servers, and resources. The critical word is logical isolation: tenants share physical or cloud compute resources, but the software enforces strict boundaries so that no tenant can see or access another’s environment.
The analogy that maps most accurately to the architecture is an apartment building. One massive high-rise building has one central foundation, one main water supply, and one security team—but inside there are separate apartments. Apartment 4B cannot see into Apartment 4C. They share the infrastructure but live in complete privacy. In PBX terms, the building is the server cluster; the apartments are the tenants; and the shared plumbing is the SIP stack, processing power, and memory that serve every customer without any customer owning or accessing those layers directly.
This stands in contrast to traditional on-premises telephony, where each business ran its own dedicated hardware. It also differs from a simple “multiple instances” approach, where providers deploy a separate virtual machine per customer—a model that may look multi-tenant from the outside but carries the operational costs of single-tenancy inside.
Multi-Tenant vs. Single-Tenant PBX: Key Architectural Differences
The choice between these two architectures shapes cost structure, scalability ceilings, security posture, and operational complexity from day one. The core distinction between multi-tenant and single-tenant PBX comes down to how an organization handles matters of growth, data safety, and budget. Here is how the two approaches compare across the dimensions that matter most to service providers and technical evaluators:
| Dimension | Multi-Tenant PBX | Single-Tenant PBX |
|---|---|---|
| Infrastructure | Shared servers, SIP stack, and database across all customers | Dedicated instance per customer—separate VM or hardware per client |
| Isolation model | Logical isolation enforced by software partitioning and access controls | Physical or virtual isolation; each instance is fully independent |
| Cost structure | Infrastructure costs amortized across multiple tenants, reducing total cost of ownership (TCO) | Larger upfront capital expenditure (CapEx) for dedicated hardware or a premium recurring fee for full isolation |
| Provisioning speed | Multi-tenant systems often go live in days or weeks | Slower; requires provisioning a full instance per customer |
| Update management | The provider rolls out new features, bug fixes, and patches centrally; all tenants benefit without scheduling upgrades | Updates must be managed per instance; risk of version fragmentation |
| Customization depth | Per-tenant configuration within platform limits; some constraints on system-level changes | Bespoke workflows, custom call routing, API integrations—tailored end to end |
| Performance isolation | Resource pooling benefits idle tenants; “noisy neighbor” risk must be managed with QoS policies | Without “noisy neighbors,” guaranteed resource reservations and performance metrics |
| Compliance suitability | Strong for most use cases; regulated industries (healthcare, finance) may require additional controls | Regulated industries—healthcare (HIPAA), finance (PCI-DSS), government—where data isolation is critical often prefer or require this model |
| Best fit | VoIP service providers, MSPs, ITSPs, hosted PBX operators managing many SME clients | Large enterprises, high-volume call centers, organizations with bespoke compliance requirements |
Neither model is universally superior. The choice between single-tenant and multi-tenant IP PBX systems depends on the specific needs of the organization or service provider. Both have advantages and disadvantages. For providers whose business model depends on serving dozens or hundreds of SME customers from a central platform, however, true multi-tenancy is the only architecture that delivers the economics and operational simplicity that makes that model viable.
How Multi-Tenancy Works: Shared Infrastructure with Logical Isolation
The engineering challenge in multi-tenant PBX is straightforward to state and demanding to execute: use one system to serve many customers, without any customer ever touching another’s data, calls, or configuration. The solution lies in a layered architecture with distinct roles at each level.
The Three-Layer Control Model
The master node (super admin) is the level accessible only to the multi-tenant PBX provider. From here, the provider creates new tenants, sets global limits such as maximum concurrent calls, and manages billing. Below that sits the tenant partition layer, and within each partition, an optional reseller or tenant admin layer.
When a new client is onboarded, the system carves out a virtual slice of the PBX. This partition includes its own database tables or distinct identifiers for users, CDRs (Call Detail Records), and configurations. From the tenant’s perspective, the system looks and behaves exactly like a dedicated PBX. They see only their own extensions, call queues, IVRs, and recordings—because the platform enforces strict namespace separation at the data layer.
A multi-tenant architecture uses a single instance of a software application to serve multiple customers. In this model, tenants share common system components—such as security mechanisms, business logic, and resource management—while remaining logically isolated from one another. This isolation ensures that each tenant’s data, configuration, and operational settings remain private and secure.
Shared Resources and Efficient Utilization
The expensive parts—the processing power, the memory, the SIP stack that handles calls—are shared. This ensures that if one tenant is idle, their allocated processing power can be used by another tenant who might be experiencing high call volume. This statistical multiplexing is fundamental to the cost advantage of multi-tenancy: rather than provisioning dedicated capacity for each tenant’s peak usage, providers size shared resources for aggregate demand, which is almost always lower than the sum of individual peaks.
True Multi-Tenancy vs. Multi-Instance Pseudo-Tenancy
One distinction worth understanding before evaluating platforms: true multi-tenancy is not the same as running many separate PBX instances managed through a shared portal. Unlike pseudo multi-tenant PBXs, which are actually multiple instances of PBX systems managed through a centralized portal, true multi-tenant architecture offers centralized control while ensuring that each tenant has complete autonomy over their configurations, data, and settings—as if their PBX were hosted on a dedicated instance. All tenants are fully isolated, with no visibility into each other’s data or settings. The distinction matters because pseudo-tenancy carries the operational burden of single-tenancy (patching each instance, managing separate configurations) without the economic benefits of true shared infrastructure.
Why Service Providers Need Multi-Tenant Architecture
Multi-tenancy is not a feature for service providers—it is the operational foundation that makes a hosted PBX business viable at scale. For cloud PBX service providers and managed service providers (MSPs), a true multi-tenant architecture is not optional—it is essential. It enables providers to host and manage PBX services for multiple customers efficiently, while maintaining strict tenant isolation, predictable performance, and scalable operations. Without multi-tenancy, providers would be forced to deploy and manage separate PBX instances per customer, dramatically increasing cost, complexity, and time to market.
The Unit Economics of Hosted PBX
Consider what deploying a single-tenant environment per customer actually costs. In a single-tenant environment, if an ITSP has 1,000 customers, they are managing 1,000 virtual machines. The licensing costs for the operating systems alone would be astronomical. Add the engineering time for patching, monitoring, and troubleshooting each instance, and the margin on any per-seat subscription evaporates quickly. Multi-tenancy collapses those 1,000 management surfaces into one, with a centralized control plane that applies patches, scales resources, and monitors health across the entire customer base simultaneously.
Hosted UCaaS solutions let smaller businesses replace capital-heavy PBX systems with predictable monthly fees, yielding up to 55% cost savings over premises-based telephony. For providers, the shared infrastructure model is what makes those competitive subscription price points achievable while still generating margin. That market opportunity is significant: SMEs represent the fastest-growing UCaaS user cohort, posting a 27.8% CAGR from 2024 to 2030.
Onboarding Speed and Operational Simplicity
Speed of customer onboarding is a direct competitive differentiator in the hosted PBX market. Efficient provisioning means quickly onboarding new clients by creating new tenant instances with pre-defined templates or custom configurations. With a well-built multi-tenant platform, provisioning a new business customer goes from a multi-day infrastructure project to a task measured in minutes. That velocity compounds: a provider that can onboard in hours versus days can handle the same sales volume with less operational staff, or higher sales volume with the same team.
A unified dashboard lets providers oversee all tenants, monitor system health, and manage resources from one central point. Software updates and security patches apply to the core system, benefiting all tenants simultaneously. That single-pane-of-glass management is a material operational advantage over managing a fleet of independent instances.
At Gama Infotech, our multi-tenant IP PBX platform is engineered specifically for VoIP providers and MSPs who need to serve multiple clients from a single, centralized infrastructure without sacrificing per-tenant control or isolation.
Core Features and Per-Tenant Configuration Options
A production-grade multi-tenant PBX exposes a broad feature set at both the platform level (controlled by the service provider) and the tenant level (configured independently by each customer). The exact split between these layers defines how much self-service providers can offer without creating support burden on themselves.
Platform-Level Features (Provider-Controlled)
At the top of the hierarchy, the service provider controls infrastructure parameters that affect all tenants: global concurrent call limits, SIP trunk allocation, system-wide security policies, software version management, billing engine configuration, and reseller hierarchy setup. Each tenant can have its own admin dashboard, call routing, and billing structure, all within a single infrastructure. The provider also manages the white-label layer—branding the portal with a custom domain and logo so that end-customer tenants experience a fully branded product.
Per-Tenant Configuration Options
Within their partition, each tenant administrator operates with substantial autonomy. While operating on a shared core system, each tenant functions as an independent PBX. This means unique extensions, IVRs, call queues, music on hold, outbound/inbound routes, and security settings can be configured for each individual client. Typical per-tenant configuration options include:
Telephony fundamentals: Extension management, DID (Direct Inward Dialing) number assignment, SIP trunk allocation per tenant, inbound and outbound call routing rules, dial plan configuration, and least-cost routing (LCR) settings.
Call handling and automation: Multi-level IVR trees with custom audio prompts, ACD (Automatic Call Distribution) queue strategies, call forwarding, call transfer, call parking, ring groups, call recording rules, and voicemail-to-email delivery.
User and device management: Extension creation and deletion, role-based access levels (tenant admin vs. standard user), softphone credential provisioning, and endpoint auto-provisioning via Zero Touch Provisioning (ZTP). The efficiency of a multi-tenant platform relies on offloading work to the customer. Modern systems provide granular tenant admin portals—a customer can reset their own passwords, change IVR greetings, and add extensions without ever calling technical support.
Billing and reporting: Per-tenant billing allows telecom companies to charge tenants separately for their usage, including voice and data services. This feature supports usage-based billing, subscription plans, or tiered pricing models, streamlining revenue generation for each tenant. Call detail records (CDRs), usage dashboards, and real-time call monitoring are typically scoped to each tenant so that tenant administrators can manage their own accounts without provider intervention.
Unified communications extensions: Unified communication features—like call routing, SMS, team messaging, contact center, and voice and video meetings—can all run in one powerful multi-tenant PBX. This positions a well-built platform as a full UCaaS delivery vehicle, not merely a voice system.
Security, Isolation, and Compliance Considerations

Security in a multi-tenant environment carries a dual responsibility: protecting each tenant from external threats (SIP fraud, DDoS attacks, unauthorized registration) and preventing any cross-tenant exposure where one customer’s data or calls could reach another. Both failure modes are serious, and both require deliberate architectural decisions rather than after-the-fact bolt-ons.
Logical Isolation at the Data Layer
The genius of multi-tenant architecture lies in logical isolation. Even though data resides on the same physical server or cloud cluster, the software strictly partitions data so that one tenant can never access another tenant’s data. In practice, this means separate database schemas or row-level security policies per tenant, distinct namespaces for CDRs and recordings, and access control systems that validate tenant context on every API call. Multi-tenant IP PBX software ensures that each tenant’s data is isolated. No client can access another’s information. This addresses security concerns and allows telecom service providers to serve multiple clients securely on a shared platform.
Network-Level Isolation and SBC Deployment
At the network layer, a Session Border Controller (SBC) is the standard mechanism for enforcing security at every SIP peering point. In multi-tenant setups, tenant-specific encryption enforcement allows each client’s communications to remain isolated and secure. Each tenant’s data and call traffic must be fully segregated using virtualized SBC sessions and VLAN segmentation. One client’s internal calls should never traverse another tenant’s network, preventing accidental exposure or leakage.
Toll Fraud and SIP Attack Prevention
In a shared environment, the blast radius of a security incident can extend beyond the compromised tenant. Service providers running multi-tenant infrastructure face a scenario where a single compromised endpoint can affect every customer on the platform. A toll fraud attack originating from one subscriber’s misconfigured PBX can generate tens of thousands of dollars in fraudulent charges before anyone notices. A DDoS attack targeting the provider’s SBC or registrar can take down voice service for every tenant simultaneously.
Effective defenses include per-tenant concurrent call limits that cap the blast radius of a compromised account, anomaly detection for unusual call patterns (particularly off-hours international traffic), TLS/SRTP encryption on all SIP signaling and media paths, and Fail2Ban or equivalent rate-limiting on SIP registration attempts. Infrastructure hardening with advanced protocols including TLS/SRTP encryption, automated failover redundancy, and intelligent intrusion detection should be standard in any production deployment.
Compliance Posture
Multi-tenant PBX systems can include built-in compliance features, such as call recording, archiving, and reporting, to help businesses adhere to regulatory requirements more easily across multiple tenants. For providers serving regulated industries—healthcare (HIPAA), finance (PCI-DSS), or legal—configuring these features per tenant, rather than globally, is essential. Each tenant may face different regulatory obligations, and the platform must support that granularity without requiring provider intervention for every configuration change.
It is also worth acknowledging a genuine limitation: for industries where data protection is non-negotiable—healthcare, finance, emergency services, and government organizations—the debate over single-tenant versus multi-tenant security becomes especially critical. For many highly regulated environments, multi-tenant architecture isn’t just risky; it often fails to meet internal governance or regulatory requirements. Service providers targeting these verticals should evaluate whether a hybrid approach—multi-tenant for standard workloads, dedicated single-tenant instances for high-compliance customers—better fits their market.
Scaling a Multi-Tenant PBX: Licensing, Resources, and Capacity Planning

Multi-tenancy dramatically simplifies scaling compared to managing a fleet of single-tenant instances—but it still requires deliberate capacity planning. Providers that grow beyond their platform’s resource envelope without proactive management will encounter performance degradation that affects all tenants, not just the one driving excess load.
Concurrent Call Capacity
The core capacity constraint in any PBX platform is simultaneous call (SIM call) capacity. In a multi-tenant environment, this pool is typically shared across all tenants. Providers must size the total SIM call license—and the underlying compute—to handle aggregate peak demand with headroom. The key planning input is not each tenant’s individual peak, but the statistical distribution of peaks across the tenant base. Because tenants in different time zones or industries peak at different times, the aggregate peak is almost always lower than the arithmetic sum of individual peaks.
Tenant Count and Resource Partitioning
The number of tenants a single platform can support depends on the underlying architecture, available compute and memory, and the call volume each tenant generates. Performance-optimized platforms can support up to 50,000–100,000 simultaneous online users in a single deployment. At the other end of the spectrum, smaller deployments are viable for regional providers getting started with ten to fifty customers. The critical planning discipline is setting per-tenant resource limits—concurrent call caps, extension limits, storage quotas—so that no single tenant can monopolize shared resources.
High Availability and Redundancy
The built-in redundancy and failover capabilities in multi-tenant IP PBX systems ensure high availability and reliability. Telecom service providers can offer consistent uptime across all tenants without the need to build separate infrastructure for each. HA configurations typically involve clustered media servers, geographically distributed SBCs, and database replication. When an individual node fails, active calls and registered endpoints automatically migrate to surviving nodes—and because this failover operates at the platform level, it protects every tenant without requiring per-tenant redundancy infrastructure.
Licensing Models and Growth Economics
Licensing in multi-tenant PBX platforms typically follows one of two patterns: a pool model where a single license covers all tenants up to a defined capacity ceiling, or a per-tenant model where providers pay for each active tenant account. The pool model is generally more operator-friendly because it reduces administrative overhead and allows providers to add tenants without per-customer licensing transactions. As the business grows, providers upgrade the pool in larger increments rather than tracking individual licenses. Telecom and VoIP resellers can establish personalized pricing, branding, and billing frameworks within a single infrastructure, providing an optimal environment for expanding operations without significant investment.
Multi-tenant IP PBX systems automate provisioning processes, meaning that adding a new tenant does not require manual infrastructure work. This automation is the multiplier that lets a small operations team manage a disproportionately large customer base—the primary structural advantage that makes the hosted PBX business model attractive.
For providers evaluating how to build or deploy a carrier-grade platform, Gama Infotech specializes in VoIP and cloud PBX solutions built specifically for ITSPs, MSPs, and telecom operators who need to run scalable, white-label hosted telephony businesses.
Evaluating Multi-Tenant PBX Solutions
Choosing a multi-tenant PBX platform is one of the most consequential technical decisions a hosted telephony provider makes. The platform you deploy on shapes your cost structure, feature velocity, security posture, and the ceiling on how many customers you can serve before needing a major architectural change. The questions below cut to what actually matters:
Is it true multi-tenancy or multi-instance? Ask vendors to describe their data isolation model at the database and SIP-stack level. A centralized management portal over separate VMs is not the same as a natively multi-tenant architecture.
What are the per-tenant resource controls? Confirm that the platform lets you cap concurrent calls, extensions, and storage per tenant. Without these controls, a single high-volume tenant can degrade service for everyone else.
Does the billing engine meet your business model? Look for native support for prepaid and postpaid billing, usage-based CDR rating, per-tenant rate decks, and automated invoicing. Integrating a third-party billing system after the fact is significantly more complex than using one built into the platform.
What is the white-label and branding scope? Providers building a branded hosted PBX product need full white-label capability: custom domain, logo, portal branding, and ideally white-labeled mobile softphone apps for end users. A white-label PBX solution allows you to deliver a fully branded communication service—complete with your logo, domain, pricing, and customer touchpoints—while the underlying infrastructure is managed by the provider.
How does the platform scale? Understand the path from your initial deployment to 10x your current customer base. What changes? What gets more expensive? Are there architectural bottlenecks that require a platform migration at a certain scale?
What security controls are available? Look for TLS/SRTP encryption, per-tenant firewall rules, SBC integration, intrusion detection, and anomaly-based fraud detection. Isolation of tenants and encryption are essential for enterprise-level security.
At Gama Infotech, we work with VoIP providers, telecom operators, and MSPs to deploy and customize carrier-grade multi-tenant PBX platforms tailored to their specific business models. Whether you are launching a hosted PBX service from scratch or scaling an existing one, our team can help you evaluate architecture options, plan capacity, and build the operational workflows that make growth sustainable. Reach out to our team at sales@gamainfotech.com or call us at +1-800-581-3963 (USA) or +91 9999402116 (India) to start the conversation.
Frequently Asked Questions
What is the difference between a multi-tenant PBX and a single-tenant PBX?
A multi-tenant PBX hosts multiple business customers on shared infrastructure, with each customer logically isolated at the software level. A single-tenant PBX dedicates an entire PBX instance—its own software, database, and resources—to a single customer. Multi-tenancy is more cost-efficient and operationally scalable for service providers; single-tenancy provides stronger performance isolation and is preferred by regulated enterprises with strict compliance requirements.
How does a multi-tenant PBX keep one customer’s data separate from another’s?
Isolation is enforced at multiple layers. At the data layer, each tenant has separate database schemas or distinct row-level identifiers for users, call detail records (CDRs), voicemails, and configurations. At the network layer, SBCs enforce tenant-specific routing rules and encryption policies so that one tenant’s call traffic never traverses another’s network segment. Access control systems validate tenant context on every API and portal request, preventing any tenant administrator from viewing or modifying another tenant’s environment.
Can a multi-tenant PBX support white-label branding for service providers?
Yes. Most production-grade multi-tenant PBX platforms support white-label deployment, allowing the service provider to present the platform under their own brand—custom domain, logo, portal interface, and in some cases white-labeled mobile softphone applications. End-customer tenants experience a fully branded product and have no visibility into the underlying technology vendor.
What are the main security risks in a multi-tenant PBX and how are they mitigated?
The primary risks are cross-tenant data exposure, toll fraud originating from a compromised tenant account spreading costs to the provider, and DDoS attacks on the shared SIP infrastructure affecting all tenants. Mitigations include per-tenant concurrent call limits to cap fraud blast radius, TLS/SRTP encryption for all signaling and media, SBC-enforced rate limiting and anomaly detection, Fail2Ban for SIP registration abuse, VLAN segmentation of tenant traffic, and proactive monitoring with automated alerting on unusual call patterns.
How does capacity planning work for a multi-tenant PBX?
Capacity planning centers on aggregate concurrent call demand across all tenants, not individual peaks. Because tenants in different industries and time zones peak at different times, the aggregate peak is typically well below the arithmetic sum of all individual peaks—this statistical multiplexing is a core cost advantage of multi-tenancy. Providers also set per-tenant resource caps (concurrent call limits, extension counts, storage quotas) to prevent any single tenant from monopolizing shared infrastructure. As the customer base grows, providers scale compute, memory, and SIM call licensing in larger increments at the platform level rather than per customer.